Learn, build, and stay ahead
API documentation, threat research, and security engineering guides from the Whisper team.
Documentation
API reference, Cypher query guide, MCP setup, and integration guides. Everything you need to connect and query Whisper.
Blog
Threat research, infrastructure analysis, product updates, and security engineering insights from the Whisper team.
White Papers
In-depth research reports on internet infrastructure intelligence, threat landscape analysis, and security methodology.
Latest insights
Threat research, infrastructure analysis, and product updates from the Whisper team.
Your AI agent is only as smart as what it can see
AI agents don’t fail because of reasoning—they fail because of missing context. Without structured, connected infrastructure data, they can’t see the relationships that turn lookups into real investigations
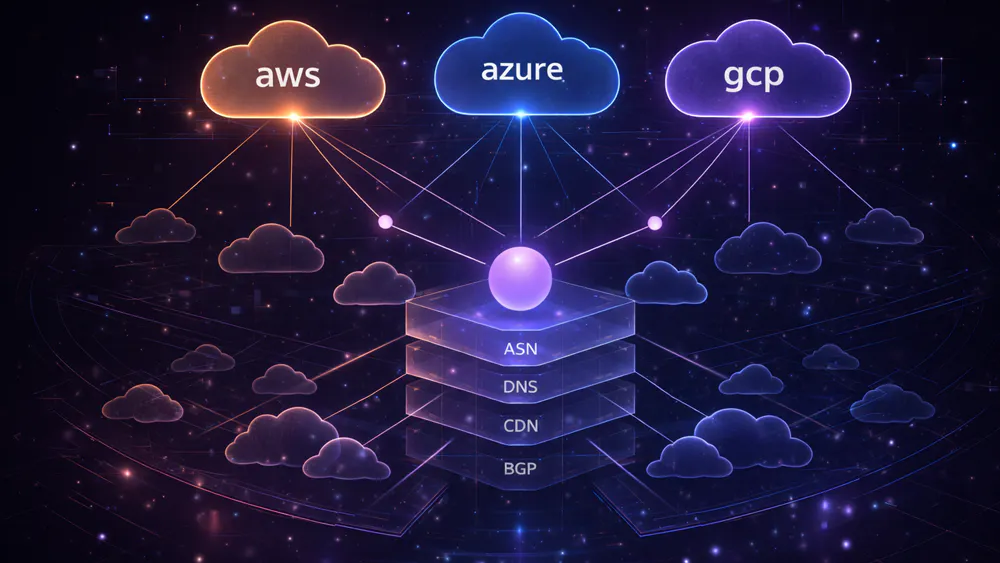
Concentration risk: when half the internet depends on three companies
Modern infrastructure looks distributed—but often isn’t. Hidden dependencies across cloud providers, DNS, and routing create concentration risk that most organisations can’t see until systems fail together

The Internet Has a Map. Most Defenders Can't Read It.
The internet’s infrastructure is public—but fragmented. Without connecting DNS, BGP, WHOIS, and certificate data, defenders see isolated signals instead of the full attack surface

Why blocklists are always one step behind
Blocklists stop domains after they’ve already been used in an attack. By mapping the infrastructure behind malicious domains, registrars, hosting, DNS, and ASNs, security teams can uncover entire campaigns instead of chasing individual indicators

One Phishing Domain Is Never Just One
Blocking one phishing domain doesn’t stop the campaign. Phishing infrastructure is built in bulk, shared registrations, nameservers, hosting, and certificates. Detecting a single domain is just the entry point to a much larger network hiding behind it.

Your Vendors' Infrastructure Is Your Attack Surface Too
Your security perimeter doesn’t stop at your firewall. Every SaaS platform, payment processor, and third-party script extends your attack surface. When their infrastructure fails or is compromised, the impact flows directly to you, often without warning.
Ready to explore the graph?
Start querying internet infrastructure data in minutes.